Table of Contents
- Understanding DDoS Attacks
- Grabify Tools and Their Impact
- The Role of IP Stressers
- IP Spoofing and Layer 4 Attacks
- IP Grabbers and Their Usage
Understanding DDoS Attacks
Modern DDoS attacks are evolving, making it essential to adopt cutting-edge protection.
Strategic defenses ensure uninterrupted operations in the face of cyber threats.
Grabify Tools and Their Impact
Grabify tools are designed to monitor and analyze traffic patterns.
They support cybersecurity measures by identifying potential threats and aiding in incident prevention.
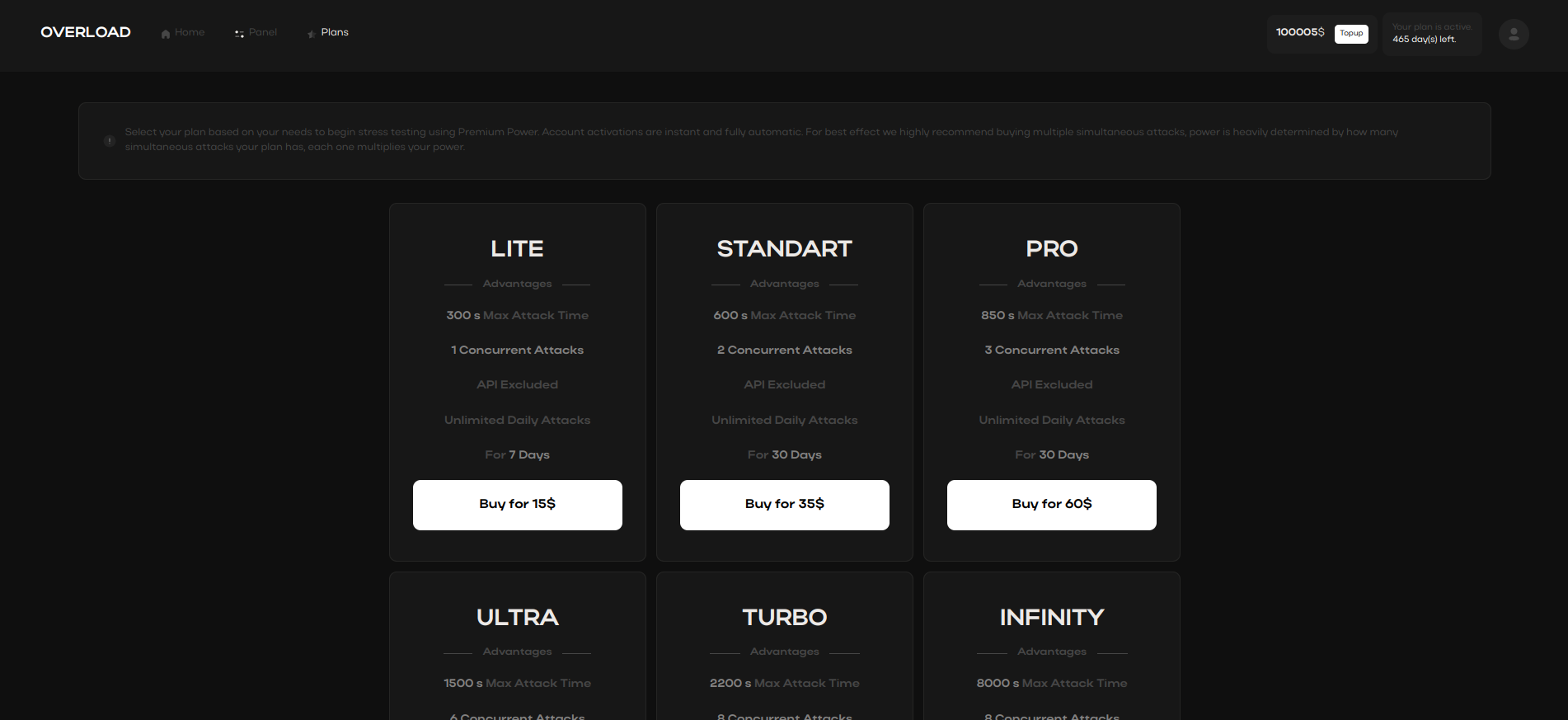
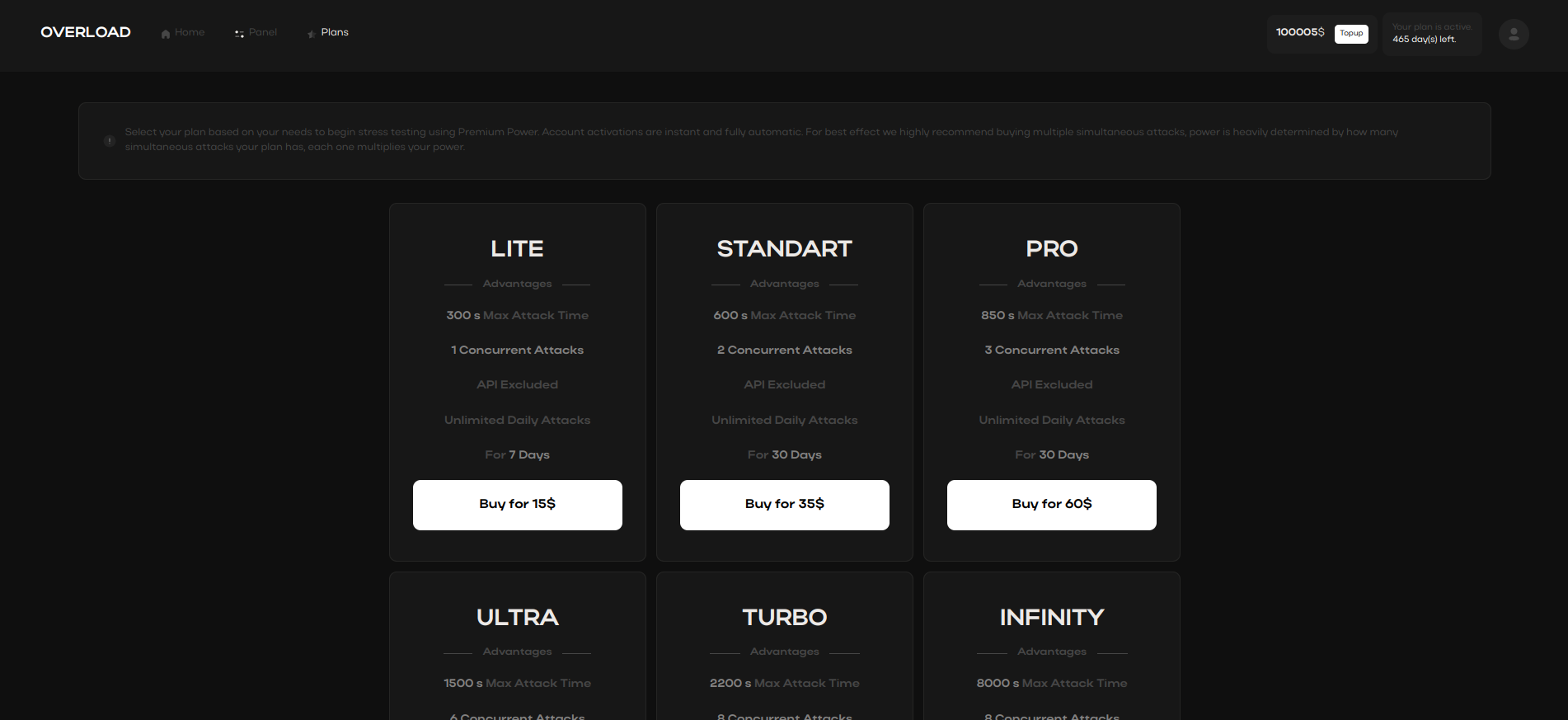
The Role of IP Stressers
Using IP stressers allows businesses to evaluate their
server capacity and strengthen network defenses against unexpected surges in traffic.
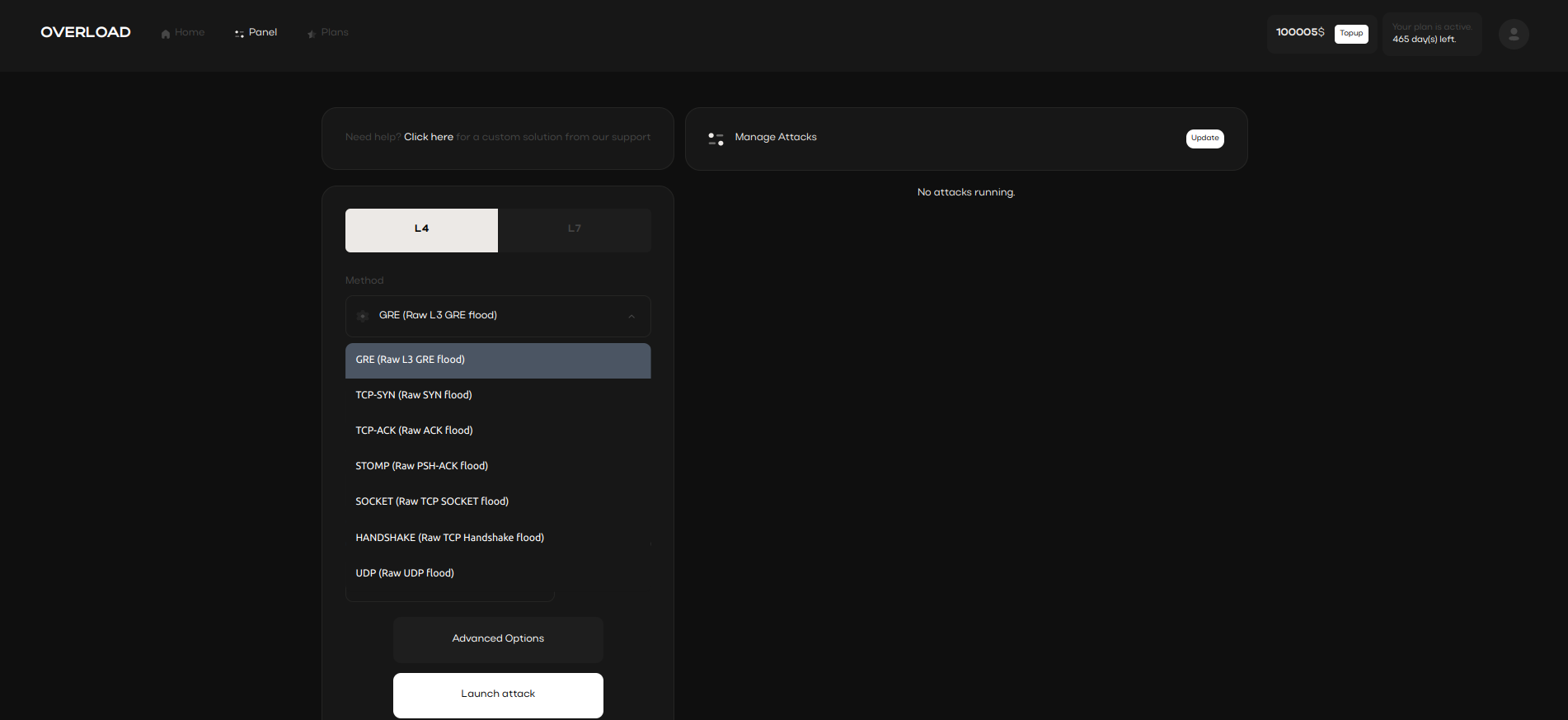
IP Spoofing and Layer 4 Attacks
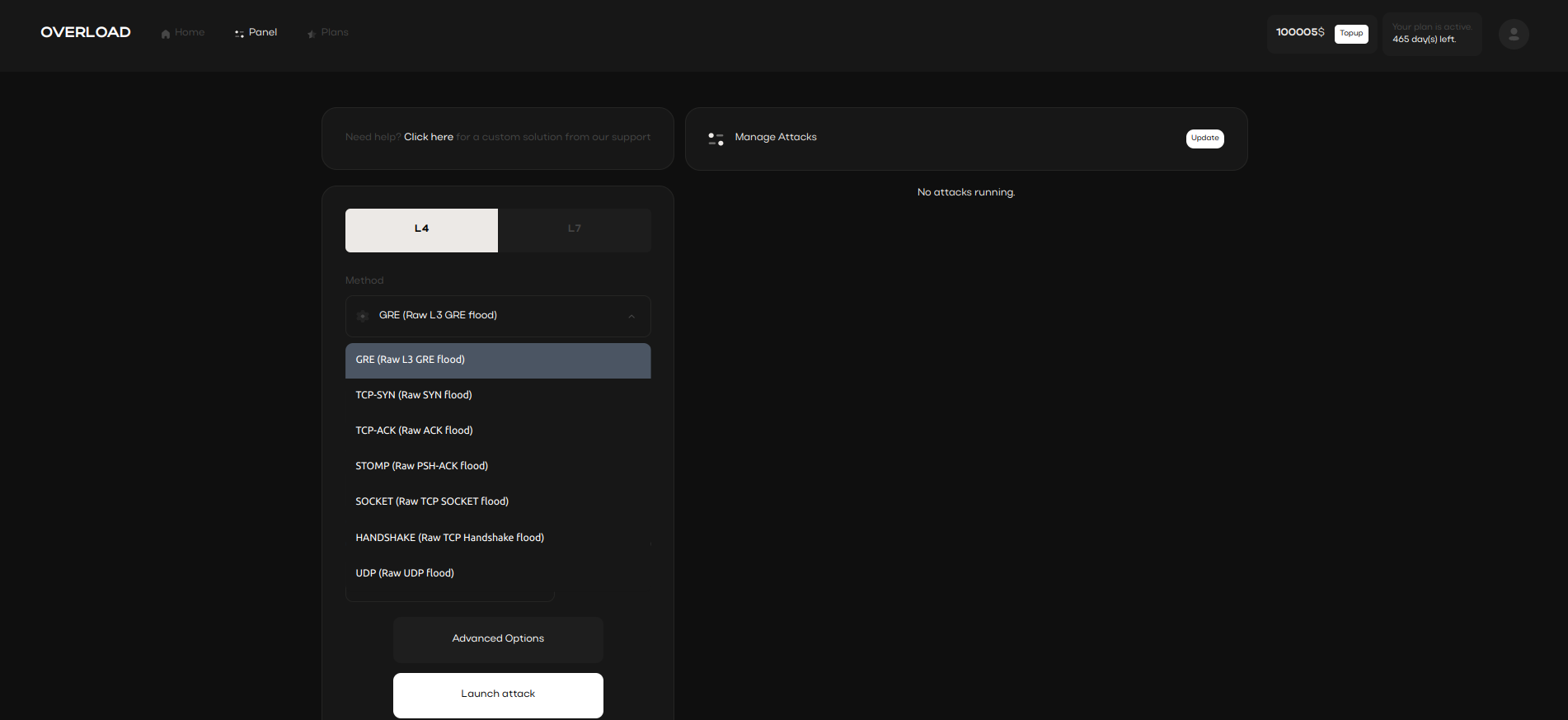
Stresser tools with IP spoofing capabilities obscure the attacker’s identity,
preventing detection and enabling secure, concealed testing. IP spoofing aids in masking attack origins,
adding a layer of anonymity during cyber evaluations.
IP Grabbers and Their Usage
IP grabbers are effective tools for extracting and analyzing network data.
They support cybersecurity efforts by identifying potential threats
and monitoring unusual activity.
stresserlab
ddos bot
lanc remastered
ddos stress
ddos attack bot
dds attack
dream stresser
vps for ddos
ilogger
quantum stresser
layer7 stresser
stresser service
nightmare stresser
stresser api
c2 ddos
stresser online
botnet ddos attack
ilogger
fortiddos
quez ip stresser
ip stresser booter free
ddos attack in cyber security